Threat Intelligence & Monitoring
We monitor threat intelligence so you don't have to. Proactive breach detection and notification service for Australian businesses.
Early Warning System for Australian Businesses
Eviant monitors global threat intelligence feeds, dark web forums, credential leaks, and breach databases to detect if Australian businesses have potentially been involved in an incident. When we identify threats relevant to your business, we reach out proactively to notify you, giving you time to respond before attackers exploit it.
Our approach combines automated monitoring with manual human analysis, to ensure these are real issues. We verify threats before reaching out and can help you respond to potential incidents.
How Our Monitoring Works
Our Services
Breach Notification Service
We monitor global threat intelligence feeds and proactively notify Australian businesses when breaches or credential leaks could impact their operations. Early warning means faster response and reduced risk.
- Credential leak detection (employee emails, passwords)
- Data breach monitoring for Australian companies
- Supply chain breach notifications
- Third-party vendor compromise alerts
Dark Web & Underground Monitoring
Threat actors discuss targets, sell stolen data, and plan attacks on dark web forums. We monitor these spaces to detect mentions of your organization before attacks occur.
- Dark web forum monitoring for company mentions
- Ransomware group target list tracking
- Stolen credential marketplace surveillance
- Early warning of planned attacks
Threat Hunting & Investigation
When we notify you of a potential breach, we don't stop there. Our team can help investigate your environment to identify if you've been compromised and find the root cause.
- Network and endpoint threat hunting
- Compromise assessment and validation
- Log analysis and anomaly detection
- Indicators of Compromise (IOC) correlation
Incident Response Integration
If a breach is confirmed, we seamlessly transition to full incident response mode—containing threats, conducting forensics, and guiding recovery efforts.
- Immediate threat containment
- Forensic investigation and evidence collection
- Remediation guidance and implementation
- Post-incident security hardening
What We Monitor
Credential Leaks
Employee email addresses and passwords exposed in breaches of third-party services (LinkedIn, Adobe, etc.)
Data Breaches
Customer data, employee records, and sensitive business information appearing in breach databases
Dark Web Mentions
Company names discussed on criminal forums, ransomware leak sites, and underground marketplaces
Supply Chain Breaches
Compromises of vendors, partners, and service providers that could impact your business operations
Ransomware Targets
Ransomware groups publicly listing Australian companies as targets or negotiation victims
Sector-Specific Threats
Emerging threats targeting specific industries operating in Australia (finance, healthcare, education, etc.)
Related Resources

My Email Was Hacked: Phishing Response for Microsoft 365
Immediate response steps for phishing attacks that compromise Microsoft 365 and Google Workspace accounts. Covers MITM phishing that bypasses MFA, removing attacker persistence, and prevention.
OpenClaw: Why You Should Avoid These AI Agents
OpenClaw and Moltbot AI agents promise productivity but introduce severe security risks. Learn why these tools threaten Australian SMBs and what to use instead.
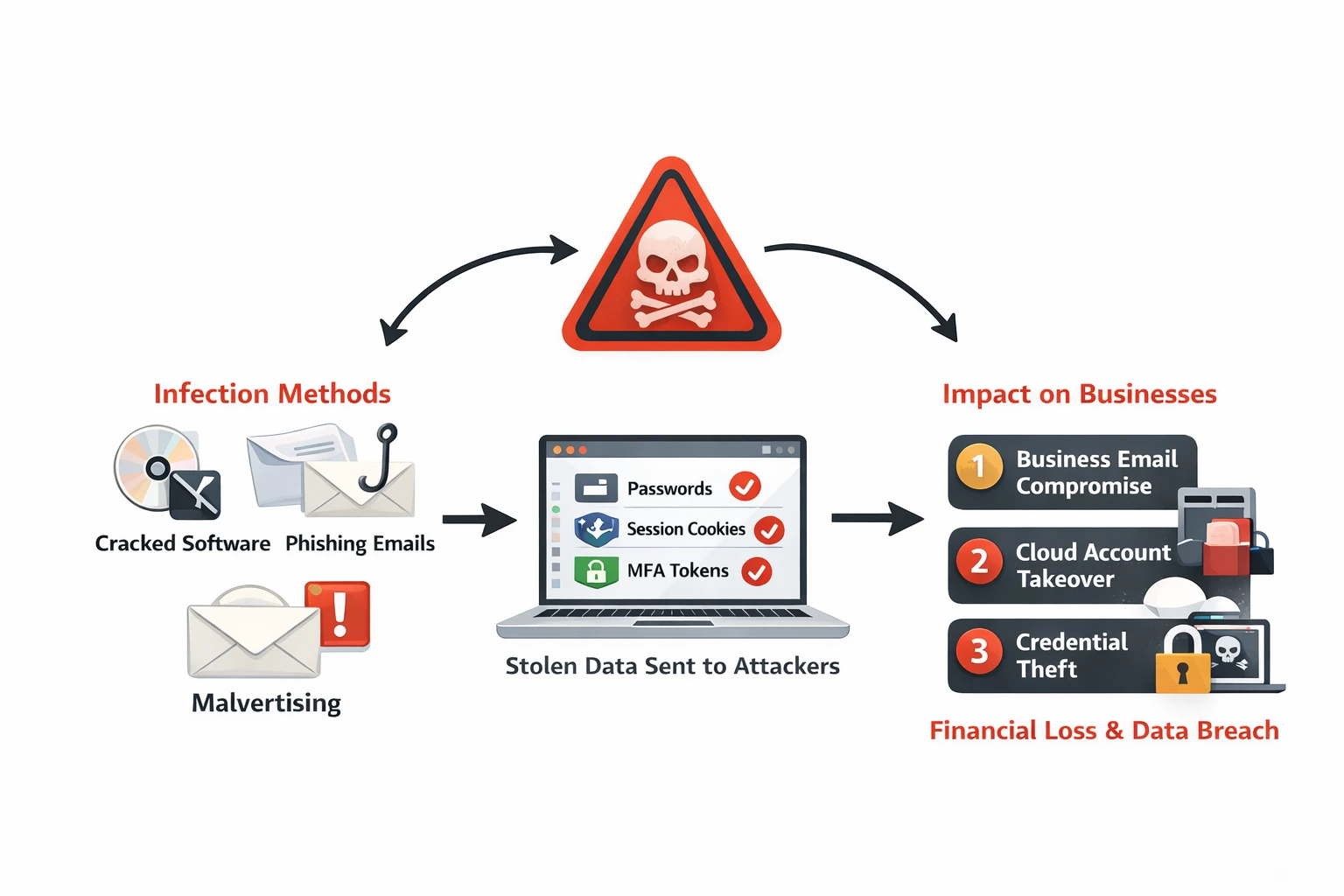
Infostealer Malware: How Credential Theft Bypasses MFA and What to Do About It
Infostealer malware silently extracts browser passwords, session cookies, and MFA tokens from employee devices. Learn how infostealers work, why they bypass security controls, and detection strategies for Australian businesses.
Get Early Warning Protection
Don't wait to discover you've been breached. Let us monitor threats and notify you before attackers strike.
